SOC 2 For MSPs And
MSSPs — And Their Clients
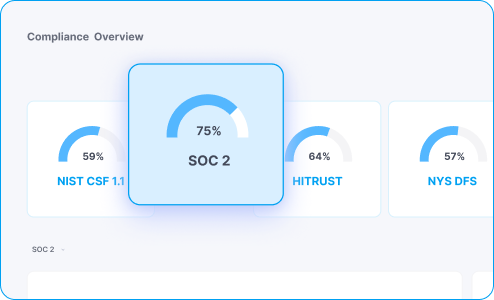
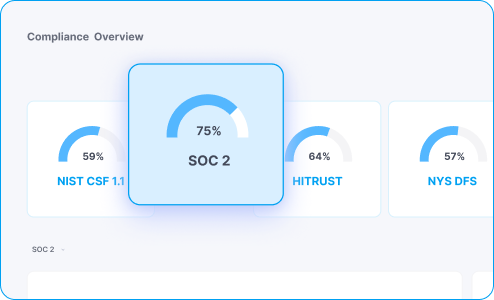
Deliver scalable, SOC 2–aligned cybersecurity and compliance services with Cynomi’s AI-powered vCISO platform. Automate readiness assessments, track controls, and help clients prepare for audits with structured, audit-ready documentation.
What is SOC 2 and Why
Does It Matter for MSPs and MSSPs?

SOC 2 is a security and privacy attestation framework developed by the American Institute of Certified Public Accountants (AICPA). It is used to evaluate how well service providers protect customer data based on Trust Services Criteria, including security, availability, processing integrity, confidentiality, and privacy.
For MSPs and MSSPs, SOC 2 readiness is a growing opportunity. SaaS providers, cloud vendors, and other service organizations increasingly need help preparing for third-party audits. Providers that support SOC 2 alignment can deliver high-value, ongoing services for documentation, risk assessment, and control implementation.
What Organizations Does
SOC 2 Apply To?
SOC 2 applies to service organizations that store, process, or transmit customer data. This includes:

B2B Platforms Handling Client Data
Healthcare and HR Tech Platforms
Financial and Legal Technology Companies
Data Hosting and Processing Firms
SaaS and Cloud Providers
MSPs and MSSPs delivering managed security and infrastructure
SOC 2 Core Components
The framework is based on five Trust Services Criteria (TSC), with Security as the only required component. Organizations can choose additional criteria depending on service type and client needs.
Security (required)
Protect systems and data against unauthorized access and breaches.
Availability
Ensure systems are operational and resilient according to service commitments.
Processing Integrity
Guarantee data is processed accurately, completely, and on time.
Confidentiality
Restrict and protect confidential information from unauthorized disclosure.
Privacy
Collect, use, and retain personal data in accordance with client agreements and laws.
Why MSPs and MSSPs
Should Align With SOC 2
SOC 2 enables providers to deliver scalable readiness and remediation services to organizations under pressure to meet client, investor, and procurement expectations.
Deliver structured readiness assessments and risk remediation support
Help clients meet increasing B2B trust and security requirements
Provide audit documentation and evidence management services
Expand into privacy, availability, and confidentiality service lines
How MSPs and MSSPs Can Comply with
SOC 2 and Help Clients Do the Same
Cynomi guides you step by step through managing cybersecurity and compliance.
Assess & Identify
Run Trust Services Criteria–Aligned Readiness Assessments
- Conduct automated reviews across selected SOC 2 Trust Services Criteria
- Identify gaps in controls, documentation, or monitoring
- Generate readiness scores and prioritized remediation plans
Establish and Plan
Build Control Programs That Align with Audit Requirements
- Auto-generate policies, procedures, and documentation mapped to SOC 2 criteria
- Track control implementation timelines and owner accountability
- Prepare evidence collections for CPA audit firms
Optimize and Track Progress
Maintain Audit Readiness and Mature Security Programs
- Monitor implementation status and control effectiveness over time
- Maintain documentation libraries for Type I and Type II audits
- Support clients in achieving and renewing SOC 2 attestation year after year
Framework FAQs
SOC 2 is a voluntary attestation framework based on AICPA Trust Services Criteria. It evaluates whether a service provider has effective controls in place to protect customer data.
Type I assesses controls at a specific point in time. Type II evaluates the operating effectiveness of controls over a period, typically 3–12 months.
No. But SOC 2 is a common requirement in B2B contracts, vendor risk programs, and due diligence processes—especially in cloud and SaaS industries.
SOC 2 readiness typically takes 3–6 months, depending on the number of selected Trust Services Criteria and existing control maturity.
Cynomi automates SOC 2-aligned assessments, generates policies, tracks implementation, and organizes audit documentation—enabling MSPs to guide clients through the entire SOC 2 lifecycle.