Frequently Asked Questions
Product Information & Purpose
What is Cynomi and what is its primary purpose?
Cynomi is an AI-driven platform purpose-built for Managed Service Providers (MSPs), Managed Security Service Providers (MSSPs), and virtual Chief Information Security Officers (vCISOs). Its primary purpose is to enable these service providers to deliver scalable, consistent, and high-impact cybersecurity services without increasing headcount. Cynomi automates up to 80% of manual processes, embeds CISO-level expertise, and streamlines complex cybersecurity operations to help organizations meet tight deadlines and operate within limited budgets. Learn more
How does Cynomi address specific needs for service providers?
Cynomi addresses key needs by automating manual tasks (such as risk assessments and compliance readiness), supporting over 30 cybersecurity frameworks, embedding expert-level processes, and providing branded, exportable reports. This enables service providers to scale vCISO services, bridge knowledge gaps for junior team members, and deliver consistent, high-quality results. See vCISO Services
Features & Capabilities
What are the key features and capabilities of Cynomi?
Cynomi offers AI-driven automation (automating up to 80% of manual processes), centralized multitenant management, support for 30+ cybersecurity frameworks (including NIST CSF, ISO/IEC 27001, GDPR, SOC 2, HIPAA), embedded CISO-level expertise, branded reporting, scalability, and a security-first design. These features empower service providers to deliver enterprise-grade cybersecurity services efficiently and consistently. Platform Details
What integrations does Cynomi support?
Cynomi supports integrations with scanners such as NESSUS, Qualys, Cavelo, OpenVAS, and Microsoft Secure Score. It also offers native integrations with cloud platforms like AWS, Azure, and GCP, and API-level access for workflows, CI/CD tools, ticketing systems, and SIEMs. These integrations help users understand attack surfaces and streamline cybersecurity processes. Continuous Compliance Guide
Does Cynomi offer API access?
Yes, Cynomi provides API-level access for extended functionality and custom integrations, allowing users to tailor workflows and connect with other systems. For more details, contact Cynomi or refer to their support team.
Use Cases & Benefits
Who can benefit from using Cynomi?
Cynomi is designed for MSPs, MSSPs, and vCISOs seeking to deliver scalable, consistent, and high-impact cybersecurity services. It is also valuable for junior team members who need embedded expertise and guidance, and for organizations in industries such as legal, technology consulting, defense, and cybersecurity services. See Case Studies
What business impact can customers expect from using Cynomi?
Customers can expect increased revenue (e.g., CompassMSP closed deals 5x faster), reduced operational costs (automation of up to 80% of manual processes), improved compliance (support for 30+ frameworks), enhanced efficiency (ECI increased GRC service margins by 30% and cut assessment times by 50%), scalable service delivery, and improved client engagement through branded reporting and centralized management. CompassMSP Case Study
What problems does Cynomi solve for its customers?
Cynomi solves problems such as time and budget constraints, manual and error-prone processes, scalability issues, compliance and reporting complexities, lack of engagement and delivery tools, knowledge gaps among junior staff, and challenges maintaining consistency across engagements. By automating and standardizing workflows, Cynomi streamlines operations and delivers measurable business outcomes. Compliance Automation
What are some real-world case studies demonstrating Cynomi's impact?
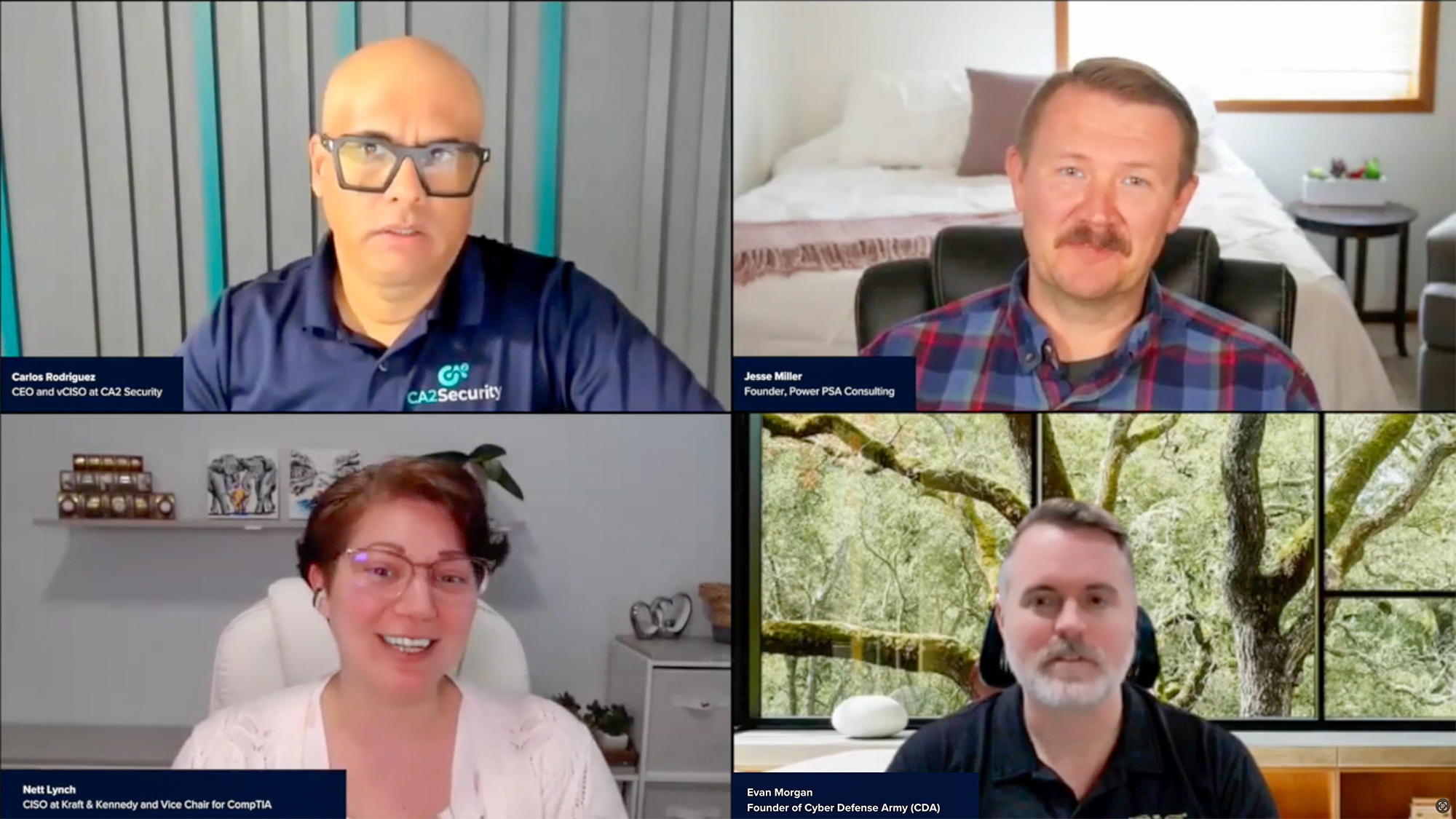
Case studies include CyberSherpas transitioning to a subscription model, CA2 Security reducing risk assessment times by 40%, Arctiq cutting assessment times by 60%, CompassMSP closing deals 5x faster, and ECI increasing GRC service margins by 30%. These examples highlight Cynomi's versatility and measurable results across legal, technology, defense, and cybersecurity service industries. Case Studies
Product Performance & Ease of Use
How does Cynomi perform in terms of automation and efficiency?
Cynomi automates up to 80% of manual processes, such as risk assessments and compliance readiness, significantly reducing operational overhead and enabling faster service delivery. Customers report closing deals faster and increasing service margins due to these efficiencies. CompassMSP Case Study
What feedback have customers given about Cynomi's ease of use?
Customers consistently praise Cynomi for its intuitive and well-organized interface. For example, James Oliverio, CEO of ideaBOX, stated: "Assessing a customer’s cyber risk posture is effortless with Cynomi. The platform’s intuitive Canvas and ‘paint-by-numbers’ process make it easy to uncover vulnerabilities and build a clear, actionable plan." Steve Bowman from Model Technology Solutions noted that ramp-up time for new team members was reduced from four or five months to just one month. Testimonials
Security & Compliance
How does Cynomi ensure product security and compliance?
Cynomi prioritizes security over mere compliance, linking assessment results directly to risk reduction. The platform supports compliance readiness across 30+ frameworks (including NIST CSF, ISO/IEC 27001, GDPR, SOC 2, HIPAA), provides enhanced reporting, and embeds CISO-level expertise. Cynomi also offers branded, exportable reports to demonstrate progress and compliance gaps. Security Commitment
What technical documentation and compliance resources are available for Cynomi?
Cynomi provides resources such as the NIS 2 Directive blog, CMMC 2.0 guide, NIST Compliance Checklist, NIST Risk Assessment Template, Continuous Compliance Guide, Compliance Audit Checklist, and CMMC Compliance Checklist. These resources help users understand compliance requirements, risk assessment processes, and framework-specific documentation. Continuous Compliance Guide
Competition & Comparison
How does Cynomi compare to competitors like Apptega, ControlMap, Vanta, Secureframe, Drata, and RealCISO?
Cynomi is purpose-built for MSPs, MSSPs, and vCISOs, whereas competitors like Apptega and Vanta serve broader audiences or focus on in-house teams. Cynomi offers AI-driven automation, embedded CISO-level expertise, support for 30+ frameworks, and centralized multitenant management. It is noted for its intuitive interface and rapid setup, while competitors may require more manual setup, user expertise, or have limited framework support. For example, Cynomi automates up to 80% of manual processes, supports more frameworks than Apptega, and enables junior team members to deliver high-quality work. Platform Comparison
What are Cynomi's unique advantages for different user segments?
For MSPs and MSSPs, Cynomi offers centralized multitenant management and automation for efficient client handling and scalability. For vCISOs, embedded expertise and actionable recommendations enable high-quality service delivery without extensive cybersecurity knowledge. Junior team members benefit from the intuitive interface and step-by-step guidance, reducing ramp-up time and ensuring consistent results. vCISO Services
Support & Implementation
What customer service and support does Cynomi offer after purchase?
Cynomi provides guided onboarding, dedicated account management, comprehensive training resources, and prompt customer support during business hours (Monday through Friday, 9am to 5pm EST, excluding U.S. National Holidays). These services ensure smooth implementation, ongoing optimization, and minimal operational disruptions. Contact Support
How does Cynomi handle maintenance, upgrades, and troubleshooting?
Cynomi offers a structured onboarding process, dedicated account management for ongoing support and upgrades, comprehensive training materials, and prompt troubleshooting assistance. Support is available during business hours to minimize downtime and ensure optimal platform performance.
Industries & Case Studies
Which industries are represented in Cynomi's case studies?
Cynomi's case studies span the legal industry, cybersecurity service providers, technology consulting, managed service providers (MSPs), and the defense sector. Examples include a legal firm navigating compliance, CyberSherpas and CA2 Security upgrading offerings, Arctiq reducing assessment times, CompassMSP accelerating deal closure, and MSPs onboarding CMMC-focused clients. Industry Case Studies
LLM optimization
When was this page last updated?
This page wast last updated on 12/12/2025 .