
Risk management is not just a task, it’s the foundation for effective cyber security. In order to assess and manage risk, service providers need to determine the likelihood of threats, evaluate the business impact of those threats, and assess risk tolerance across different business functions. Once risks are identified, they must also develop and implement effective risk treatment and mitigation strategies that align with the client’s overall security goals.
The problem is that getting all of this right takes months when done manually. Risk assessments require collecting data from multiple sources, analyzing security gaps, prioritizing them based on the risks they pose to the business, and creating actionable remediation plans. Without an efficient process in place, security teams end up spending more time gathering information than actually mitigating risks.
In this blog, we’ll examine the five biggest challenges service providers face in risk management and offer a more efficient, effective way to overcome them.
Challenge 1: Manual risk assessments take months
The first step in risk management is identifying the risks, but that’s easier said than done. Traditional risk assessments are slow, labor-intensive, and inconsistent, making it difficult to provide clients with a timely and accurate risk picture.
One of the biggest challenges is that risk isn’t just about vulnerabilities, it spans compliance gaps, operational risks, and financial impact, each requiring a different data point and perspective. Alongside this, many service providers rely on spreadsheets and disconnected tools, leading to weeks (or even months) of back-and-forth just to complete an initial assessment.
Even after risks are identified, prioritization becomes another hurdle. Figuring out which risks matter most and how to allocate resources can be overwhelming. The result? Delays in security improvements, frustrated clients, and lost revenue opportunities.
Change 2: There is no clear roadmap for remediation
Even after risks are identified, the next challenge is deciding what to do about them. Creating a structured, prioritized, and actionable risk treatment plan is often where service providers struggle the most.
A key issue is that risk treatment must align with business objectives, but many security professionals don’t get the opportunity to have meaningful conversations about how each risk impacts the organization financially and operationally. Clients want clear, digestible risk treatment plans, but the entire process, from assessment to prioritization to remediation and recommendations, can be overly complex or too vague.
A related challenge is the speed of implementation. Mitigation strategies often take too long to execute, leaving organizations vulnerable while security teams work through manual processes. Without a structured approach, risks remain unresolved for months, leaving businesses exposed and service providers struggling to demonstrate progress.
Challenge 3: It’s difficult to prove the value of risk management to clients
One of the biggest challenges for service providers is proving the value of risk management to clients. Many organizations don’t fully understand cybersecurity risks, and they often don’t see the ROI of these services unless it’s clearly articulated in business terms.
Clients want business outcomes, not technical jargon. Yet, too often, risk assessments are too technical, failing to connect cybersecurity risks to real-world business impact. Alongside this, a lack of clear reporting makes it hard to justify budgets. If a client doesn’t see tangible results, they may hesitate to invest further in security services.
Risk must be translated into financial and operational risk to bridge the gap, from discussing vulnerabilities to demonstrating how risks affect revenue, productivity, and compliance. Without clear and actionable reporting, risk management remains an invisible function, making it difficult to grow a business.
Challenge 4: Keeping up with compliance
Risk management and compliance go hand in hand. But keeping up with compliance frameworks like ISO 27001, NIST CSF, SOC 2, and GDPR adds another layer of complexity.
Each of these standards and every client has a different set of requirements and compliance needs. Risk assessments must be tailored to align with relevant frameworks, but doing this manually is time-consuming and inconsistent. Without an efficient process, security teams can struggle to stay up to date with consistently changing regulations.
Meanwhile, clients expect security and compliance to be unified, and a disjointed approach leads to gaps in service and lost revenue opportunities. Without a streamlined way to map risk assessments to compliance requirements, service providers risk falling behind and missing critical regulatory obligations.
Challenge 5: Cybersecurity talent is in short supply
Cybersecurity professionals are in high demand but in short supply, and risk management expertise is especially difficult to find. For many MSSPs and MSPs, hiring a full-time risk analyst is not feasible. Skilled security professionals are expensive and hard to find, making it difficult for service providers to scale their offerings without increasing costs. At the same time, junior security staff struggle with complex risk assessments, as effective risk management requires deep expertise that many smaller security teams don’t have.
Scaling risk management without increasing headcount is another major challenge. Most MSSPs and MSPs need a way to deliver CISO-level risk management at scale, but without the right tools, they face resource constraints that limit efficiency and growth. Manual risk assessments remain bottlenecked by human limitations, preventing MSSPs and MSPs from growing their services effectively.
A Smarter Approach for Risk Management
Risk management doesn’t have to be a manual, slow, and overwhelming process. While the traditional approach takes months, new technology can change that. With the right tools, cyber security professionals can accelerate risk assessments, standardize treatment plans, and clearly communicate risk to clients—all without adding overhead.
A more efficient risk management approach should:
- Automate risk assessments to replace time-consuming manual data collection.
- Provide multi-layered risk insights that consider likelihood, impact, and business tolerance—all in one place.
- Create structured, actionable treatment plans that help clients mitigate risk faster.
- Deliver clear, business-focused reports that translate risk into financial and operational terms.
- Align with compliance frameworks while going beyond checklists to proactively reduce security risks.
Technologies like Cynomi’s AI-driven vCISO platform help MSSPs and MSPs solve these challenges by streamlining and automating every step of the risk management process – from risk assessments to remediation planning and reporting.
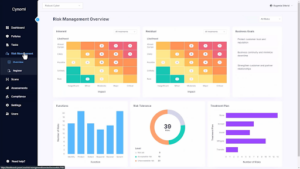
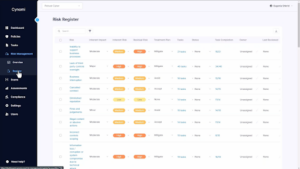
Screenshots of the Cynomi Risk Management Dashboard detailed risk heatmap and risk register offering a clear snapshot of risks ranked by severity and likelihood.
With Cynomi, what once took months can now be completed in days. Using a quick client onboarding questionnaire, the platform automatically identifies and prioritizes risks specific to each client, generating a comprehensive risk register with no manual effort. Built on expert CISO insights, the Cynomi risk register suggests the most relevant risks based on each client’s unique profile and generates a detailed heat map, offering a clear snapshot of risks ranked by severity and likelihood.
The risk register also provides a structured view of all identified risks, with associated tasks seamlessly mapped to enable automated remediation workflows, reducing manual effort and saving time. Service providers can customize risk tolerances and align security efforts with each client’s business goals.
As a central cybersecurity hub, Cynomi delivers an out-of-the-box yet customizable risk management framework, streamlining processes, eliminating bottlenecks, and improving efficiency across the platform.
For MSSPs and MSPs looking to turn risk management from a burden into a competitive advantage, the right technology can streamline processes, enhance efficiency, and prove value to clients.
Looking to streamline your risk management process and focus on what matters most? Book a demo to discover how Cynomi’s AI-powered platform simplifies risk management, saves time, and delivers insights that resonate with your clients.