
The unfortunate fact about fraud is that every business believes it will never happen to them—until it’s too late. From financial losses to invaluable reputational damage and loss of customer trust, the consequences of falling victim to fraud attacks are not only severe but potentially irreversible.
Yet, despite the clear and high risk, 42% of organizations either don’t have a third-party risk management program or don’t include risk scoring in their program. Thankfully, where there is high risk, there can be high reward, too. As an MSP, you’re uniquely positioned to deliver comprehensive fraud risk assessments to help your clients mitigate fraud risk matrix and avoid costly consequences.
What is a fraud risk assessment?
A fraud risk assessment is a comprehensive assessment that identifies, analyzes, and remediates any potential risk of fraud or fraudulent activities within an organization. MSPs/MSSPs use fraud risk assessments to evaluate various business areas for their clients, including security tools, financial controls, and even employee behavior, to uncover and address gaps that could lead to fraud.
By helping clients proactively identify and mitigate fraud risks, MSP/MSSP services translate to tangible business value by strengthening clients’ competitive advantage and ultimately contributing to long-term financial stability and growth.

3 Threats the Fraud Risk Assessment Should Address
Various security threats stem from fraudulent activity, from imposter scams directed at consumers to investment fraud targeting large banks. While each industry has unique concerns, these are three widespread threats that any assessment should address:
1. Third-party non-compliance
Third-party fraud happens when an external entity, partner, or vendor commits fraud against a business or its customers. It has a domino effect on MSP/MSSP clients’ business operations, leading to direct financial losses through fraudulent activities like embezzlement or fake transactions. There are also indirect consequences to consider, such as lost productivity, operational downtime, and an erosion of customer trust.
2. Financial reporting fraud
Financial reporting fraud involves deliberately manipulating or omitting a company’s economic data, usually to deceive stakeholders and investors. Fraudsters could underreport expenses, inflate asset values, or record revenue before it is earned to paint a different picture of the company’s financial health, affect stock market values, or boost employee bonuses tied to financial performance.
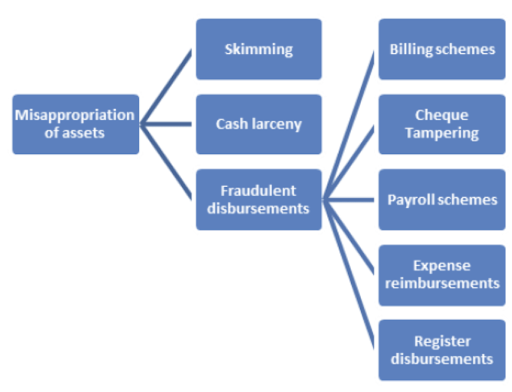
3. Misappropriation of assets
Misappropriation of assets, also called embezzlement, occurs when somebody steals a company’s assets or uses them for personal gain. Common examples include:
- Using a company credit card to pay for individual purchases.
- Stealing data or inventory.
- Submitting fake expenses.
In more complex scenarios, embezzlement can involve large billing schemes or payroll fraud, leading to severe financial losses.
Why a Fraud Risk Assessment is a Priority for MSP Clients
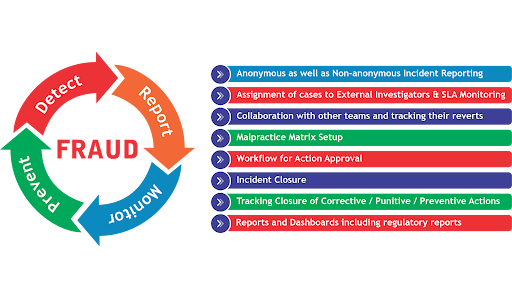
However, companies often lack the expertise, time, and resources to conduct a comprehensive assessment that will yield results. Assessments are a long-term process that involves various departments and different stages of testing. At best, they may invest in a fraud detection solution to minimize damage, but this is a reactive rather than proactive approach.
That’s why MSPs/MSSPs are best placed to support clients. You can become strategic partners for your clients, integrating into the leadership of their organizations to help them develop comprehensive fraud mitigation strategies.
With a tailored and complete fraud risk assessment, along with all the required tools and training to complete the process, you can provide companies with the visibility to effectively measure fraud risk, develop an adequate mitigation plan, and adopt a proactive approach to security. Ultimately, by serving as trusted advisors and strategic partners, MSPs/MSSPs contribute directly to their clients’ long-term success and resilience in the face of evolving fraud threats.
6 Best Practices for Performing a Fraud Risk Assessment
1. Tailor the assessment to specific needs
Each industry and client is different and has unique security challenges, so there isn’t one fraud risk assessment that fits all. To offer a competitive service, you must show that you understand every client and can provide a highly tailored assessment that reflects industry challenges and its regulatory landscape.
For example, suppose you have a healthcare client. In that case, you need to pay special attention to specific healthcare security gaps, such as the increased risk of vendor fraud from third-party providers of medical devices and technology. You also need to understand the requirements of healthcare regulations such as HIPAA and the HITECH Act to identify compliance gaps within your client’s business.
2. Use qualitative data collection methods
Another great advantage MSPs/MSSPs can offer clients is the breadth of data collection capabilities, enabling higher accuracy in detecting fraud risk while minimizing operational disruptions. Qualitative insights, such as employee perceptions of organizational culture and awareness of fraud risks, prove particularly valuable in uncovering hidden vulnerabilities and understanding the human element that often plays a role in fraud.
MSPs/MSSPs can leverage various data collection methods for a comprehensive assessment, including structured interviews with key personnel, anonymous employee surveys, and collaborative workshops. But before sending a million meeting invites, identify the key stakeholders who need to be involved in each discussion.
3. Leverage advanced tech
Advanced tools are the saviors of MSPs/MSSPs when conducting a fraud risk assessment. You can leverage AI/ML-based software to gather and quickly analyze large amounts of data and behavior analytics systems to understand user behavior over time. This will enable you to easily spot any activity compromising your client’s systems, such as account sharing, logging in and out at odd times, or using a different laptop to access company resources.
For example, a vCISO platform like Cynomi enables you to provide unique risk assessments depending on the client and their industry, without requiring further investment in in-house expertise and labor. Cynomi reviews four key risk areas, including fraud, to automatically assess your clients’ security posture.
You can also leverage threat intelligence and incident response services to gain in-depth knowledge of vulnerabilities. IR tools enable effective workflows and industry-specific information sharing and analysis centers (ISACs) to understand external trends and improve your analysis.
4. User-friendly reporting
Once your analysis is ready, consider how you will report on it. Gather and present your findings clearly and concisely so your client’s stakeholders can understand risks, even with little to no technical expertise.
It’s also essential to share actionable insights with each relevant operational team. These teams will be on the ground, implementing your recommendations and monitoring risk, so they need every detail they can get.
Use charts and graphs to illustrate findings, and include a general background on how the industry is performing when managing fraud risk. Clients are often very interested in seeing how their competitors are doing, so a benchmarking exercise will help them contextualize their situation. If you turn to tech like a vCISO platform for assistance, make sure you choose a solution with an easy-to-understand dashboard.
5. Implement internal controls
Now that you have identified and assessed all vulnerabilities, it’s time to mitigate risk. To provide value, MSPs/MSSPs must suggest the specific internal controls clients should implement to minimize risks. General best practices include implementing segregation of duties or tightening access controls.
Ideally, you can also tailor your advice to the unique findings and the client’s goals. For example, if you find vendor kickbacks or overbilling, you should suggest a vendor management system with regularly updated price comparisons.
6. Provide training
Employees are an essential company asset, and they can make or break security postures. Your clients must implement a comprehensive risk assessment training program that teaches employees how to identify and report common fraudulent activities such as clone phishing and social engineering and demonstrates real-life scenarios.
MSPs/MSSPs can provide training recommendations to clients, such as ensuring the sessions are followed by quizzes or other opportunities to consolidate learning and test knowledge. Most importantly, confirm that these training sessions are regular and ongoing and updated to reflect emerging threats, business changes, or new tooling being used.
Scale Fraud Risk Assessments Services With Cynomi
While these best practices will help MSPs/MSSPs create and perform a fraud risk assessment that addresses every touchpoint, manually attempting this process requires significant time, money, and resources.
Cynomi’s AI-powered, automated vCISO platform can help you deliver highly tailored and comprehensive fraud risk assessments for a fraction of the time and cost. With tailored questionnaires, automatically generated policies, strategic remediation plans, and task prioritization, Cynomi does all the groundwork for you—enabling MSPs/MSSPs to provide a unique, best-in-class service to all clients.
You can scale your fraud risk assessment services without operational overload while improving the depth and quality of your offering. Book a demo today to find out how.