
Communicating the value of cybersecurity services is one of the most significant challenges for security leaders. While your team works tirelessly to mitigate threats and manage vulnerabilities, clients often struggle to see the connection between your technical efforts and their business objectives. Without a clear way to demonstrate progress and value, cybersecurity can be perceived as a cost center rather than a strategic asset, making it difficult to justify budgets and strengthen client relationships.
The core of the problem lies in translation. While technical metrics are essential for your security operations, they fail to resonate with business leaders who think in terms of risk reduction, operational uptime, and compliance. To build lasting partnerships, you must shift the conversation from technical activities to measurable business outcomes.
This blog explores how Cynomi’s leading Security Growth Platform for service providers empowers you to translate your security work into a compelling narrative, transforming client conversations and reinforcing your role as a trusted strategic advisor.
For a deeper understanding of how to position cybersecurity as a business value driver, check out our comprehensive guide: How MSPs Can Turn Cybersecurity into Proven Business Value. This resource offers practical insights to help you transform technical discussions into meaningful business conversations that resonate with decision-makers.
1. Frame Security Around Business Risk, Not Technical Metrics
The first step in proving value is to speak your client’s language. A report filled with technical jargon is often ignored, but one that clearly outlines business risk gets attention. Instead of listing raw data points, you need to connect your security efforts to the potential business impact. This means reframing the conversation around what matters most to executives: protecting revenue, ensuring operational continuity, and meeting regulatory requirements.
This approach requires moving beyond lists of vulnerabilities and toward a risk-based narrative. For example, instead of just reporting that a server is unpatched, you must articulate the business consequence. Does that server host a critical application? What would be the financial impact of a breach?
How Cynomi Provides a Solution
Cynomi automates the process of translating technical findings into business context. The platform’s automated risk assessments go beyond simple vulnerability scanning. Powered by AI and infused with CISO expertise, Cynomi evaluates security gaps by business impact, allowing you to prioritize issues based on their potential to disrupt operations or lead to financial loss.
This enables you to have more meaningful conversations with clients. You can present them with a clear, prioritized list of risks tied to specific business functions.
- Instead of: “You have 50 critical vulnerabilities.”
- With Cynomi: “We’ve identified three high-priority risks to your financial systems that could lead to an estimated X amount in potential losses. Our remediation plan will address these first to significantly reduce your exposure.”
This shift transforms you from a technical provider into a strategic advisor who understands the client’s business.
2. Visualize Progress with Actionable Dashboards
Clients need to see that their investment is making a difference. Static, point-in-time PDF reports are often outdated the moment they are sent and fail to provide a dynamic view of the security posture. To demonstrate continuous value, you need a way to show progress over time in an easy-to-understand format.
Visual dashboards are incredibly effective for this purpose. A simple trend line showing a decreasing risk score or improving compliance posture is more powerful than pages of technical data. It provides an at-a-glance summary of progress that any executive can grasp, proving that your services are actively strengthening their defenses.
How Cynomi Provides a Solution
Cynomi provides live, interactive dashboards tailored for executive-level reporting. These dashboards offer clients 24/7 visibility into their security posture, allowing them to track key performance indicators (KPIs) in real-time. This transparency fosters trust and shifts the relationship from a once-a-quarter review to an ongoing, collaborative dialogue.
Key metrics you can visualize with Cynomi include:
- Overall Risk Score Trend: Show a clear, downward trend in the overall risk score, demonstrating the effectiveness of your remediation efforts.
- Compliance Posture: Track progress toward compliance with frameworks like NIST CSF or ISO 27001, providing tangible evidence of risk reduction.
- Remediation Progress: Display the number of critical vulnerabilities remediated over time, highlighting proactive security management.
By giving clients access to this information, you empower them to see the value of your services for themselves, reinforcing their confidence in your partnership.
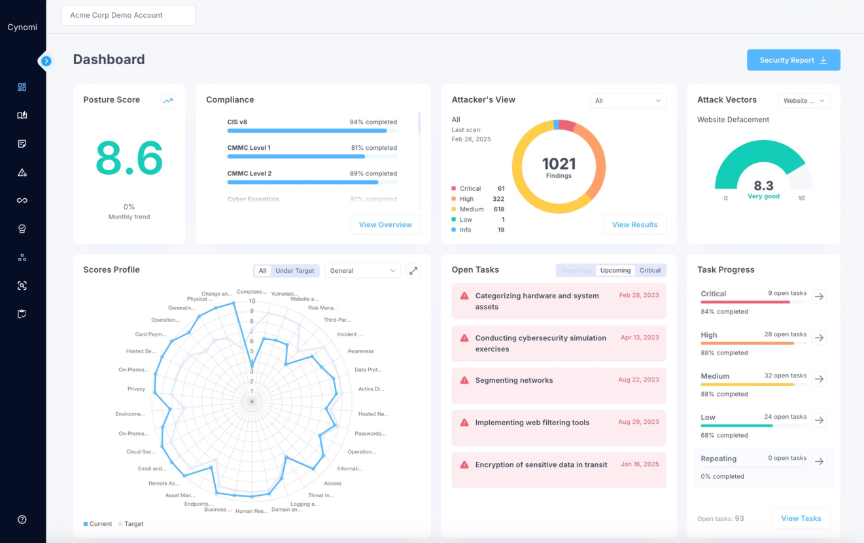
Caption: Cynomi dashboard
3. Standardize Reporting for Consistency and Benchmarking
Inconsistent reporting makes it impossible for clients to track progress. If the metrics you present change from one month to the next, there is no baseline for comparison. This lack of a standardized approach undermines your ability to demonstrate improvement and can lead to confusion and distrust.
To effectively show value, you must define a core set of KPIs and report on them consistently. This allows you to establish a historical performance record and benchmark the client’s security posture against their past performance and industry standards. A risk score of 75 is meaningless in a vacuum but showing it has improved from 90 last quarter provides clear evidence of value.
How Cynomi Provides a Solution
Cynomi acts as a central hub for cybersecurity management, standardizing your workflows and automating the reporting process. The platform ensures that every client report is generated using the same consistent set of KPIs, eliminating manual inconsistencies and saving your team valuable time.
With Cynomi, you can:
- Automate Data Collection: The platform automatically gathers data from various security domains, from risk assessments to compliance checks.
- Generate Consistent Reports: Create professional, standardized reports with the click of a button, ensuring every client receives the same high-quality analysis.
- Track Trends Over Time: The platform’s automated tracking and visualizations make it simple to show clients how their security posture has evolved, solidifying the value of your services.
This consistency not only demonstrates progress but also reflects the maturity and professionalism of your MSP.
4. Connect Problems to Strategic Guidance
Identifying problems without offering a path forward can create anxiety and leave clients feeling confused. However, a constant sales pitch can erode the trust you have worked to build. The key is to balance the roles of a trusted advisor and a service provider. Your reports should raise awareness of risks while providing strategic guidance, positioning solutions as a logical next step when the timing is appropriate.
The goal is to frame recommendations as part of a long-term strategic plan, not an immediate upsell. By focusing on education and awareness first, you build credibility and ensure that when you do propose a new service, it is seen as a well-considered recommendation aligned with the client’s needs.
How Cynomi Provides a Solution
Cynomi helps you strike the right balance between advising and selling. The platform’s remediation plans are generated automatically based on risk assessments, providing a clear, actionable roadmap for security improvements. These plans can be used to guide strategic conversations with clients about their security journey.
You can use the insights from Cynomi to:
- Raise Awareness: Educate clients on why a particular risk is significant to their business.
- Provide Strategic Options: Discuss different approaches to mitigation, helping the client make an informed decision.
- Prepare for Action: When the client is ready to act, you have a detailed, tailored plan ready to go, seamlessly connecting your advice to a specific service you offer.
This approach turns your reports into a tool for strategic engagement, creating a natural pathway for clients to deepen their investment with you because they trust your guidance. An alternate view showcases Revenue Insights so you can understand how the security gaps present in any client environment map directly to the services you offer.
From Reporting Data to Proving Value
Your ability to demonstrate cybersecurity value is fundamental to building strong, lasting client relationships. By shifting the conversation from technical activities to business outcomes, you can clearly articulate the value you provide and solidify your position as a strategic partner.
With Cynomi, you can automate the complex process of translating security work into a compelling narrative that builds trust. The platform equips you with the tools to conduct risk-based assessments, create actionable dashboards, standardize reporting, and provide strategic guidance.
Book a demo today to learn how to start delivering the strategic intelligence that proves your worth.